New Phishing Threat: Astaroth Bypasses Two-Factor Authentication in Real Time
Phishing attacks have become increasingly sophisticated, and while many individuals can identify the more obvious attempts, new methods are emerging that are harder to detect. One such method involves a phishing kit known as Astaroth, which can completely circumvent the protective barrier of two-factor authentication (2FA) through real-time credential interception and session hijacking.
Understanding the Astaroth Phishing Kit
Astaroth represents a significant evolution in phishing tactics. Unlike traditional phishing schemes that rely on fake login pages, Astaroth acts as a middleman between your device and legitimate authentication services, such as Gmail, Yahoo, and Microsoft. This means that, during the attack, it can capture everything in real time, including sensitive information, effectively bypassing 2FA completely and granting attackers unauthorized access to your accounts.
-
Easy Internet Sleuthing Techniques You Wish You Knew Sooner

-
How to make money on TikTok and YouTube Shorts if you don’t know how to edit

-
Finnish Researchers Develop Eco-Friendly Method to Extract Silver Using Kitchen Ingredients

-
AI Takes Flight: U.S. Fighter Pilots Navigate Sky Battles with Artificial Intelligence

How the Attack Unfolds
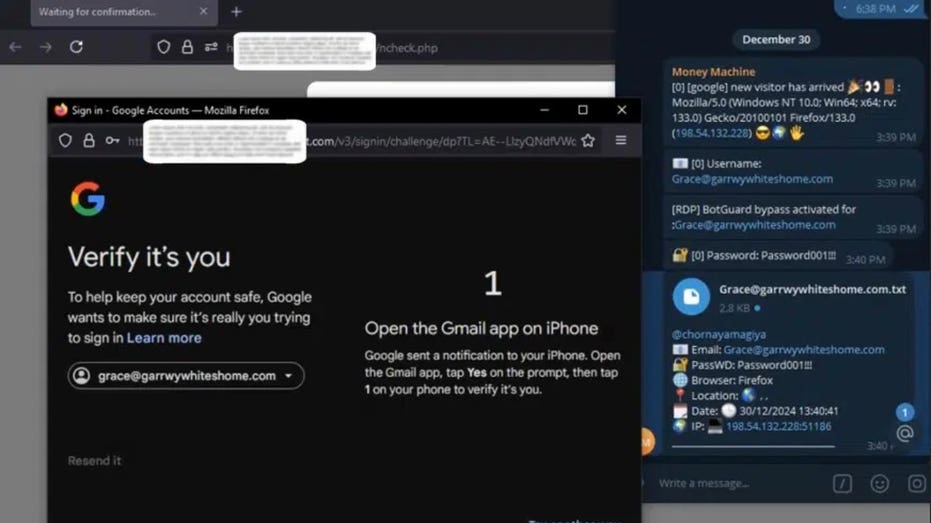
The attack begins when a user clicks on a phishing link that directs them to a malicious website, which is designed to look identical to the legitimate site. Since these malicious sites often possess valid SSL certificates, there are no apparent red flags or security warnings to alert the victim. When a user enters their login credentials—including username, password, device information, and IP address—Astaroth captures this data before forwarding the request to the legitimate site.
The Phishing Kit and Two-Factor Authentication
Astaroth is particularly dangerous because it does not regard 2FA as an obstacle. The tool intercepts one-time passwords immediately upon entry, regardless of whether they are sent via an authenticator app, SMS, or push notification. The stolen codes are then rapidly transmitted to the attacker through a web panel or a Telegram alert, allowing them to exploit the credentials before they expire.
Additionally, Astaroth can capture session cookies, which are small data packets that keep users logged in after authentication. By injecting these cookies into their own browsers, attackers can access accounts without needing to provide passwords or 2FA codes, effectively bypassing all security measures.
What Makes Astaroth Stand Out
According to cybersecurity experts at SlashNext, Astaroth distinguishes itself from traditional phishing kits through its capability to intercept credentials in real time, automate attacks, and resist takedown efforts. Unlike its predecessors that depend on tricking users into inputting their credentials on fake sites, Astaroth eliminates that step, making it a more streamlined and effective tool for cybercriminals.
Features that Attract Cybercriminals
Astaroth’s appeal to cybercriminals is further enhanced by its robust features. The kit employs bulletproof hosting to maintain its online presence despite law enforcement actions, receives frequent upgrades to evade security patches, and follows a structured payment model. For a price of $2,000, buyers can access six months of continuous updates. Additionally, the creators allow potential buyers to test the kit before purchase, building trust in its effectiveness.
Astaroth is readily available on Telegram and various underground cybercrime forums, making it challenging for authorities to track its distribution and use.
Recognizing Signs of a Phishing Attack
Awareness of potential phishing signs is crucial in protecting yourself from these sophisticated attacks. Look out for:
1. Unexpected account logins or security alerts.
2. Unexplained logouts from accounts.
3. Password changes or settings updates that you did not initiate.
4. Sluggish system performance or unusual behavior.
5. Browser issues or strange activity.
6. Unfamiliar programs or scripts running in the background.
Strategies to Safeguard Your Information
To enhance your security against attacks like Astaroth, consider implementing these strategies:
1. **Avoid Unknown Links and Use Strong Antivirus Software**: Remember that many attacks require user interaction to be successful. By refraining from clicking unknown links and investing in reliable antivirus software, you can shield yourself from potential threats.
2. **Double-Check Website Addresses**: Always verify URLs and utilize bookmarks for sites you trust. Instead of clicking links in emails, manually type in the web address or use a trusted bookmark to minimize the risk of encountering malicious pages.
3. **Keep Your Devices Updated**: Regularly updating your operating system and applications ensures that security vulnerabilities are patched, making it harder for malware to exploit weaknesses.
4. **Utilize Passwordless Authentication**: Whenever possible, opt for passwordless login methods such as passkeys, Google Sign-In, or Apple Sign-In. These methods utilize cryptographic key pairs, significantly reducing the chances of your login information being intercepted.
Conclusion: Stay Informed and Vigilant
Astaroth is a stark reminder of how phishing tactics are evolving to exploit security measures like 2FA. As cybercriminals become more adept, it is essential for individuals and organizations to stay informed about these threats and adopt modern security practices. By utilizing passwordless logins, keeping software up to date, and remaining vigilant, you can better protect yourself against sophisticated cyber threats.
What measures do you think governments and companies should take to protect individuals from advanced phishing attacks like Astaroth? Share your thoughts with us, and stay updated on the latest tech tips and security alerts by subscribing to our newsletter.